This website uses cookies for security purposes only. We do not track you or see your data.
ePsiLoN
-

Old Wanda experiment
I just realised I never put a post about one of my favourite projects – Wanda the fish – web…
-

Back to blogging
It has been 8 years since I last posted here. A lot has happened in the technology and the cybersecurity…
-

OWASP guide v4 application testing checklist-tracker
This is a simple tracker I have created to facilitate the process of appetising so I do not lose myself…
-

Autodafe fuzzer compile fix
I wanted to take a look at an old fuzzer called AutoDafe because its name popped up in several papers…
-

Maritime Cybersecurity Mind Map
Recently I have been researching the cyber threats in the maritime industry, what has been done and which areas are…
-

Stack canaries cartoon
Lately I have been busy studying different buffer overflow protection mechanisms and while reading about stack canaries a funny picture…
-

DLink dir655 rev B firmware reverse engineering – part 1
Intro Recently I stumbled upon Paul dot com blog post Reverse Engineering Firmware Primer and decided to see if I…
-

Setting up capstone (Debian Wheezy)
Intro Recently I’ve decided to dedicate a fresh Debian environment for my RE tools and having binwalk seemed as a…
-

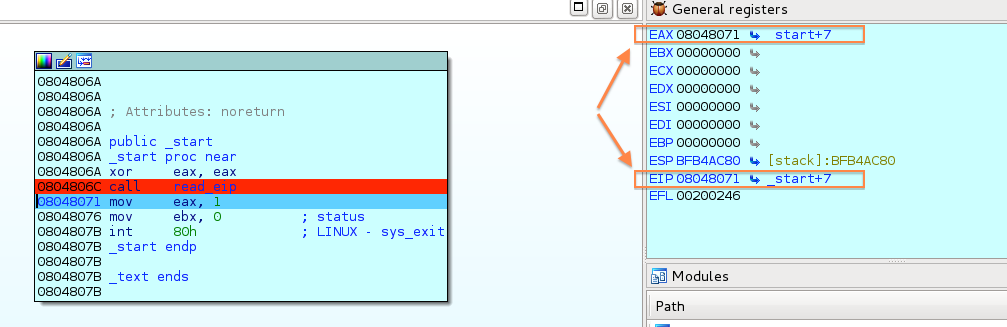
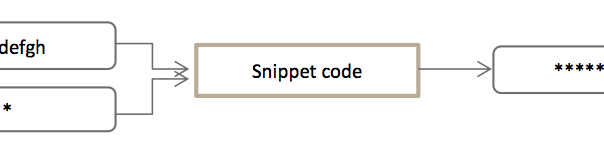
Practical Reverse Engineering Exercises – Ch1-Ex2 – Write-Up
Intro This is the second post of a blog series following my progress with the “Practical Reverse Engineering: x86, x64,…
-

Practical Reverse Engineering Exercises – Ch1-Ex1 – Write-Up
Intro This is the first post of what should be a blog series following my progress with the “Practical Reverse…